In today’s fast-paced world, free USB charging stations have become a staple in airports, hotels, and shopping centers. They offer a quick power boost to essential devices. However, these convenient charging points harbor hidden dangers.
The FBI recently highlighted the risks associated with these stations, warning that they could be a gateway for cybercriminals to install malware on your devices. This tactic, known as “juice jacking,” turns a simple charge into a significant security risk.
FBI’s Warning Lights

“Bad actors have figured out ways to use public USB ports to introduce malware and monitoring software onto devices,” states a warning on X from the FBI’s Denver field office. This announcement wasn’t based on a specific incident but served as a preventive advisory.
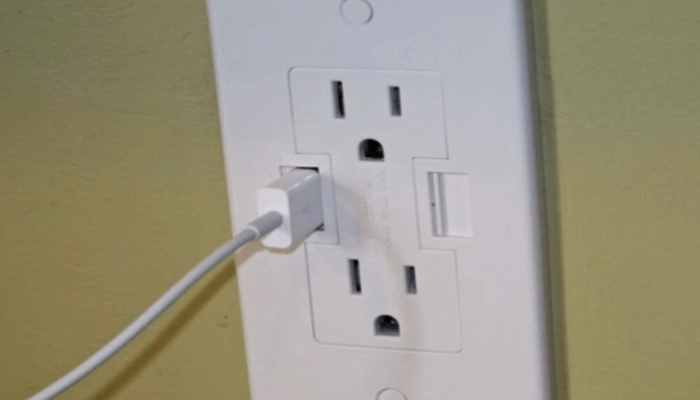
The FBI emphasizes the importance of avoiding these free charging stations and suggests carrying your own charger and using an electrical outlet instead.
Understanding ‘Juice Jacking’
“Juice jacking” might sound playful, but there’s nothing fun about it. This cyber theft method involves criminals loading malware onto public USB charging stations.
When an unsuspecting user plugs in their device, it becomes infected. This malware can lock the device or export sensitive information, such as personal data and passwords, directly to the perpetrator. This can lead to unauthorized access to online accounts and a plethora of other cyber threats.
A Brief History of Public Charging Woes

The concept of juice jacking isn’t new. The Federal Communications Commission (FCC) has been warning about this potential threat since 2021. They advised against the use of public charging stations due to the risk of hijacking consumer devices.
Though technically possible, the FCC states that there are no confirmed instances of juice jacking. However, the mere possibility presents a clear and present danger to public cyber safety.
Real Risks and Hypothetical Horrors

Cybersecurity experts have proven that juice jacking is more than just a theoretical threat; it’s a practical reality demonstrated through various proofs of concept.
However, despite its feasibility, there hasn’t been a surge in reported cases (via CNBC). This discrepancy might lead some to underestimate the risk, but it’s essential to stay vigilant.
Protecting Your Device

Travelers can take several steps to protect themselves from juice jacking. First, prefer AC power outlets over USB ports for charging devices in public places.
Carrying an external battery pack or a charging-only cable — which does not allow data transfer — can also be a game-changer. These cables, available from trusted suppliers, ensure that your device can be charged without risking data exposure (via FBI).
Making the Right Connections

If you find yourself needing to use a USB port, be mindful when your device asks you to select between “share data” and “charge only.” Always opt for “charge only” (via FCC).
This simple choice can be the difference between securing your personal information and exposing it to potential theft. Paying attention to these prompts can help safeguard your data from unauthorized access.
Beyond the Cord: Public Wi-Fi Hazards

The danger doesn’t end with USB charging stations. Public Wi-Fi networks present another significant risk, offering a perfect hunting ground for cybercriminals (via FBI).
These networks, often unsecured, can be exploited to intercept personal information. To protect your data from prying eyes, it’s crucial to avoid performing sensitive transactions, like online shopping or banking, on public Wi-Fi networks.
Personal Cybersecurity Hygiene
Good cybersecurity habits can help protect you from various threats. To fend off malicious software, keep your device’s software up to date and install reputable antivirus programs.
Creating strong, unique passphrases for each online account can also significantly reduce the risk of unauthorized access, especially if one account gets compromised.
Email and Website Scams

Be wary of phishing scams. Scrutinize every email and text message you receive, especially those urging you to take immediate action.
Examine the sender’s email address and the URL of any linked websites closely. Scammers often mimic legitimate sites or email addresses with slight variations in spelling to deceive their victims into providing sensitive information.
Financial Foresight

When making online purchases, use a credit card for an added layer of protection against fraud. Credit cards often offer better fraud protection compared to other payment methods.
Additionally, be cautious about sharing your financial information online, especially with unknown or unverified sources. Always double-check before proceeding with online transactions.
Stay Charged and Secure
Staying charged is essential, but so is staying secure. While public USB charging stations offer convenience, they also pose significant security risks.
By using your own charging devices, being cautious with public Wi-Fi, and practicing good cybersecurity hygiene, you can reduce the risk of exposing your sensitive information to hackers.
